Public Key Authentication
From Luke Jackson
(diff) ←Older revision | Current revision | Newer revision→ (diff)
OpenSSH is a FREE version of the SSH connectivity tools that technical users of the Internet rely on. For more information on OpenSSH check out their website OpenSSH
Contents |
Introduction
Users of telnet, rlogin, and ftp may not realize that their password is transmitted across the Internet unencrypted, but it is. OpenSSH encrypts all traffic (including passwords) to effectively eliminate eavesdropping, connection hijacking, and other attacks. Additionally, OpenSSH provides secure tunneling capabilities and several authentication methods, and supports all SSH protocol versions.
Another great feature about OpenSSH is the Public Key Authentication mechanism. With this feature enabled you are able to securely authenticate to servers with out typing in a password.
Requirements
- Linux/Unix/Mac OS X
- openssh
- openssh-server
- openssh-clients
This tutorial will assume that you already have the above installed and operating correctly. I will use Fedora Core 3 as the Linux distribution so if you are using something different your file paths may be different.
Generate Key Pair (Linux/Unix/Mac OS X)
This can be accomplished on either the server or the client. In this tutorial it is done on the server for simplicity. If you do not have access to the server you will have to send your public key file to someone that does and have them import it for you.
Open a shell and ensure you are in your home directory.
To confirm this your prompt should look something like this [root@server.ext ~]#.
If the ~/.ssh directory does not exist create it using the commands below:
mkdir .ssh cd .ssh
Locate the command ssh-keygen:
Usage: ssh-keygen [options] Options: -b bits Number of bits in the key to create. -c Change comment in private and public key files. -e Convert OpenSSH to IETF SECSH key file. -f filename Filename of the key file. -g Use generic DNS resource record format. -i Convert IETF SECSH to OpenSSH key file. -l Show fingerprint of key file. -p Change passphrase of private key file. -q Quiet. -y Read private key file and print public key. -t type Specify type of key to create. -B Show bubblebabble digest of key file. -C comment Provide new comment. -N phrase Provide new passphrase. -P phrase Provide old passphrase. -r hostname Print DNS resource record. -G file Generate candidates for DH-GEX moduli -T file Screen candidates for DH-GEX moduli
In this tutorial I will use a key type of RSA you are welcome to explore the different types but for my needs RSA is more than capable.
Create your key pair by executing the following command:
ssh-keygen -f <filename> -t dsa -b 1024
You will be prompted to enter a passphrase THIS IS IMPORTANT!!! If you forget your passphrase the key pair is lost forever please choose a passphrase you will not forget!
Generating public/private rsa key pair. Enter passphrase (empty for no passphrase): *********** Enter same passphrase again: *********** Your identification has been saved in <filename>. Your public key has been saved in <filename>.pub. The key fingerprint is: **:**:**:**:**:**:**:**:**:**:**:**:**:**:**:** root@server.ext
You should now have 2 files in your ~/.ssh directory:
- <filename> - Private Key
- <filename>.pub - Public Key
Generate Key Pair (Windows)
It is also possible to do this on a Windows compatible OS using PuTTYgen.
Configure SSH Daemon (Linux/Unix/Mac OS X)
Open the file /etc/ssh/sshd_config and browse to the section displayed below:
# Authentication: #LoginGraceTime 2m #PermitRootLogin yes #StrictModes yes #MaxAuthTries 6 RSAAuthentication yes PubkeyAuthentication yes AuthorizedKeysFile .ssh/authorized_keys
Ensure that the last 3 parameters are set like above and then save your changes.
You will have to restart the SSH daemon for your changes to take effect. You can do so with the command below:
/etc/init.d/sshd restart
If it completes successfully you should see something similar to the output below:
[root@server.ext ~]# /etc/init.d/sshd restart Stopping sshd: [ OK ] Starting sshd: [ OK ]
Configure User (Linux/Unix/Mac OS X)
Since root is the most powerful user it will be used in this tutorial. if you wish to enable authentication for another user follow these steps and replace root with the desired username.
Return back to your home directory and check to see if you have a file named authorized_keys in sub-directory called .ssh.
If you don't no problem just create them like so:
mkdir .ssh cd .ssh touch authorized_keys
Now add the public key to the authorized_keys file. This may seem easy but it is the most common place for error. If you miss copy one character it will not authenticate you.
To prevent any errros cat the contents of your public key (<filename>.pub) to the authorized_keys file.
cat ../<filename>.pub > authorized_keys
Should you be in a situation where you have to copy and paste the key from one server to another insure that the key file looks identical to the original. This will save you many hours of troubleshooting as there is no log entry telling you the public key was copied incorrectly.
Ensure the ownership is set to root and the permissions are 644 with the commands below:
chown -R root:root ~/.ssh chmod -R 644 ~/.ssh
Configure Client (Linux/Unix/Mac OS X)
Open a shell and ensure you are in your home directory.
If the ~/.ssh directory does not exist create it using the command below:
mkdir .ssh
Copy the private key to the client using the commands below:
cd .ssh scp root@server.ext:.ssh/<filename> identity
Ensure the ownership is set to root and the permissions are 644 with the commands below:
chown -R root:root ~/.ssh chmod -R 644 ~/.ssh
Find the command ssh-agent:
Usage: ssh-agent [options] [command [args ...]] Options: -c Generate C-shell commands on stdout. -s Generate Bourne shell commands on stdout. -k Kill the current agent. -d Debug mode. -a socket Bind agent socket to given name. -t life Default identity lifetime (seconds).
You will need to bind the ssh-agent to your current shell with the command below:
ssh-agent $SHELL
Next locate the command ssh-add:
Usage: ssh-add [options] Options: -l List fingerprints of all identities. -L List public key parameters of all identities. -d Delete identity. -D Delete all identities. -x Lock agent. -X Unlock agent. -t life Set lifetime (in seconds) when adding identities. -c Require confirmation to sign using identities
By default ssh-add will look in the identity file for you private keys.
Add you private key to the agent with the command below:
ssh-add
You should be prompted for your passphrase similar to the output below:
[root@client.ext .ssh]# ssh-add Enter passphrase for /root/.ssh/identity: Identity added: /root/.ssh/identity (/root/.ssh/identity)
Now you are ready to connect to the remote server with your private key.
[root@client.ext .ssh]# ssh root@server.ext Last login: Sun Oct 8 07:45:16 2006 from 127.0.0.1 [root@server.ext ~]#
Configure Client (Mac OS X) (GUI)
Open a shell and ensure you are in your home directory.
If the ~/.ssh directory does not exist create it using the command below:
mkdir .ssh
Copy the private key to the client using the commands below:
cd .ssh scp root@server.ext:.ssh/<filename> identity
Ensure the ownership is set to root and the permissions are 644 with the commands below:
chown -R root:root ~/.ssh chmod -R 644 ~/.ssh
Requirements
- Mac OS X 10.4.X+
- Built-in Terminal Application
- SSH-Agent Client - Download
Install SSH-Agent
Install the SSH-Agent you downloaded from the requirements section.
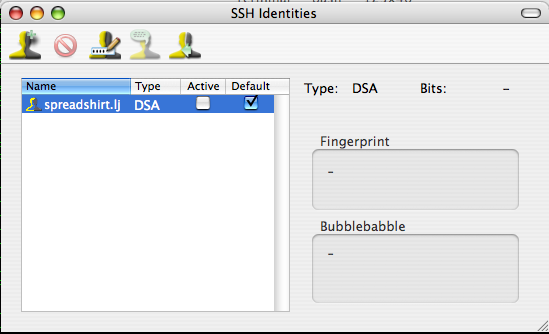
You will have to launch the application and configure some settings before it is ready for use. Click on View from the menu and select Show SSH Identities. Find your identity file and ensure Default is checked. Next select SSH Agent from the menu and choose Preferences. Ensure that Activate Default Identities is enabled when launched. Close SSH-Agent.
It may be useful to have on the dock, this way you can easily activate keys by simply clicking once and entering your passphrase. Launch SSH-Agent one last time and it should prompt you for your passphrase and activate your ID.
Once this is completed you can close the identities window and test your connection with the open terminal window.
[root@client.ext .ssh]# ssh root@server.ext Last login: Sun Oct 8 07:45:16 2006 from 127.0.0.1 [root@server.ext ~]#
Configure Client (Windows)
It is also possible to do this on a Windows compatible OS using PuTTY and Pagent.